Exclusive, explosive reports from the patriot
Joint U.S.-French Intelligence Task Force,
operating on American soil for over 200 years
Joint U.S.-French Intelligence Task Force,
operating on American soil for over 200 years
TOM
HENEGHAN INTELLIGENCE BRIEFINGSALL Patriot Americans MUST know with
sources insideAmerican/European intelligence agencies and
INTERPOLreporting what is really going on behind the scenes of
thecorporate-controlled, fascist, extortion-friendlypropaganda U.S.
media's massive deceptionsProtect and defend YOUR Constitution
Bill of Rights,the Supreme Law of the United
Stateshttp://www.tomheneghanbriefings.com/https://twitter.com/Tom_Heneghan
THE NAZI BUSH-CLINTON NSA FACES U.S. MILITARY DECAPITATION
by Tom Heneghan, International Intelligence Expert





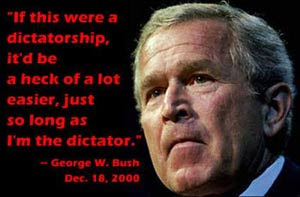
If this image does not appear due to hacking click to view
George W. Bush on 5/21/99 "There ought to be limits to freedom"
http://parapolitics-info.
George W. Bush on 5/21/99 "There ought to be limits to freedom"
http://parapolitics-info.
UNITED States of America - It can now be reported that the U.S. NAZI Paperclip NSA, CIA and the TREASONOUS UN-Constitutional Department of Homeland Security (DHS) have declared MARTIAL LAW on American soil and now have 100% control of the U.S. corporate extortion-friendly media filth.

NAZI German 93-year old sociopath George Herbert Walker Bush has gone vile threatening to have his political opponents assassinated and threatening to use a 9-11 style FALSE FLAG attack (bio-chemical) on the American People if the U.S. Military Flag Officers refuse to capitulate in what will be a rigged and stolen 2016 presidential election on behalf of daddy Bush’s CIA Mena, Arkansas, drug trafficking business partners Hillary and Bill Clinton.
The U.S. Military Flag Officers have responded with a direct threat to get physical with the Bushes and Clintons and the U.S. corporate, extortion-friendly media elite within 24 hours unless they stand down and immediately surrender ending NAZI Paperclip NSA-CIA occupation of the United States of America.
Yes, folks, it is about to get physical, so lock and load.
Note: NAZI German daddy Bush aka George H.W. Bush, who had President John F. Kennedy assassinated, and attempted to have President Ronald Reagan assassinated, scripted the 1980 “October Surprise”; hired Bill Clinton as his Mena, Arkansas drug trafficking and foreign currency laundry business partner; and finally, helped script the blatant THEFT of the year 2000 presidential election on behalf of his deviate son, junior George W. BushFRAUD, remains the DIRECT ENEMY of the American People and their sacred U.S. Constitution and American Republic.
The U.S. Military Flag Officers have concluded that NAZI German George Herbert Walker Bush will be held accountable and dealt with immediately with due prejudice.
In closing, daddy Bush has gone vile reference the Russian Federation Tesla technology audit of the year 2000 presidential election that proves that the U.S. NSA blatantly STOLE the year 2000 presidential election from then Vice President now year 2000 DULY ELECTED President Albert Gore Jr. of Carthage, Tennessee, along with the fact that the Russian Federation now has photographs of junior BushFRAUD having hot homosexual sex with White House prostitute Jeff Gannon and lifelong lover, former Yale University roommate, Victor Ashe.
The Russian Federation also has recently obtained videos of Bush Crime Family CIA business partner, Nazi Jew neocon Hillary Rodenhurst Clinton engaging in hot lesbian sex aka raping a 9-year old girl named Kathy O’Brien.
Reference: The U.S. Secret Service is ready to unload not only on Bush and Clinton but on the corporate CIA-controlled homosexual media that has enabled:
- the DESTRUCTION of the United States of America,
- the LOOTING of the U.S. Treasury,
- the DESTRUCTION of our electoral process,
- the WRECKING of the U.S. economy,
- criminal UNCONSTITUTIONAL wars, and
- the SHREDDING of our U.S. Constitution protected freedoms and privacy, the Supreme Law of our Land
Final message to the NAZI Paperclip Bush-Clinton-NSA-CIA-DHS crime syndicate:
Prepare for your worst nightmare: American-French revolutionary style Jacobinian rage.

Air-Raid Sirens in San Diego and Tacoma; Fighter Jets Seen Scrambling, Reports of "Explosion Sounds"
- Oct 13, 2016
3:24 AM EDT 13 October 2016 -- Numerous reports began filtering into
SuperStation95 about two hours ago that air raid sirens were blaring in
San Diego, CA, with one reader sending us ...
https://www.superstation95.John St. Clair Akwei vs.NSA, Ft. Meade, MD, USA
Evidence for the Lawsuit filed at the US courthouse in Washington, D.C.
(Civil Action 92-0449)
John St.Clair Akwei vs. NSA Ft George G. Meade, MD
My knowledge of the National Security Agency's structure,
national security activities, proprietary technology,
and covert operations to monitor individual citizens.
==========
The NSA's mission and the NSA's domestic Intelligence operation.
Communications Intelligence (COMINT)
Blanket coverage of all electronic communication in the U.S. and the world to ensure national security. The NSA at Ft. Meade, Maryland has had the most advanced computers in the world since the early 1960's. NSA technology is developed and implemented in secret from private corporations, academia, and the general public.
Signals Intelligence (SIGINT)
The Signals Intelligence mission of the NSA has evolved into a program of decoding EMF waves in the environment for wirelessly tapping into computers and tracking persons with the electrical currents in their bodies.
Signals Intelligence is based on the fact that everything in the environment with an electric current in it has a magnetic flux around it which gives off EMF waves. The NSA/DoD has developed proprietary advanced digital equipment which can remotely analyze all objects whether man-made or organic that have electrical activity.
Domestic Intelligence (DOMINT)
The NSA has records on all U.S. citizens. The NSA gathers information on U.S. citizens who might be of interest to any of the over 50,000 NSA agents (HUMINT). These agents are authorized by executive order to spy on anyone. The NSA has a permanent National Security Anti-Terrorist surveillance network in place. This surveillance network is completely disguised and hidden from the public.
Tracking individuals in the U.S. is easily and cost-effectively implemented with the NSA's electronic surveillance network. This network (DOMINT) covers the entire U.S., involves tens of thousands of NSA personnel, and tracks millions of persons simultaneously. Cost effective implementation of operations is assured by NSA computer technology designed to minimize operations costs.
NSA personnel serve in Quasi-public positions in their communities and run cover businesses and legitimate businesses that can inform the intelligence community of persons they would want to track. N.S.A. personnel in the community usually have cover identities such as social workers, lawyers and business owners.
Individual citizens occasionally targeted for surveillance by independently operating NSA personnel.
NSA personnel can control the lives of hundreds of thousands of individuals in the U.S. by using the NSA's domestic intelligence network and cover businesses. The operations independently run by them can sometimes go beyond the bounds of law. Long-term control and sabotage of tens of thousands of unwitting citizens by NSA operatives is likely to happen. NSA Domint has the ability to covertly assassinate U.S. citizens or run covert psychological control operations to cause subjects to be diagnosed with ill mental health.
NSA's domestic electronic surveillance network
As of the early 1960's the most advanced computers in the world were at the NSA, Ft. Meade. Research breakthroughs with these computers were kept for the NSA. At the present time the NSA has nanotechnology computers that are 15 years ahead of present computer technology.
The NSA obtains blanket coverage of information in the U.S. by using advanced computers that use artificial intelligence to screen all communications, irregardless of medium, for key words that should be brought to the attention of NSA agents/cryptologists. These computers monitor all communications at the transmitting and receiving ends. This blanket coverage of the U.S. is a result of the NSA's Signals Intelligence (SIGINT) mission.
The NSA's electronic surveillance network is based on a cellular arrangement of devices that can monitor the entire EMF spectrum. This equipment was developed, implemented, and kept secret in the same manner as other electronic warfare programs.
With this technology NSA personnel can non-obtrusively tap into any communication device in existence. This includes computers, telephones, radio and video-based devices, printers, car electronics, and even the minute electrical fields in humans (for tracking individuals).
Signals Intelligence Remote Computer Tampering
The NSA keeps track of all PCs and other computers sold in the U.S. This is an integral part of the Domestic Intelligence network.
The NSA's EMF equipment can tune in RF emissions from personal computer circuit boards (while filtering out emissions from monitors and power supplies). The RF emission from PC circuit boards contains digital information in the PC. Coded RF waves from the NSA's equipment can resonate PC circuits and change data in the PC's. Thus the NSA can gain wireless modem-style entry into any computer in the country for surveillance or anti-terrorist electronic warfare.
Radio and Television signals can be substituted at the receiving end with special EMF equipment. Replacing signals in Radios and Televisions is another outgrowth of the NSA's Signals Intelligence (SIGINT) mission.
Detecting EMF Fields in Humans for Surveillance.
A subject's bioelectric field can be remotely detected, so subjects can be monitored anywhere they are. With special EMF equipment NSA cryptologists can remotely read evoked potentials (from EEGs). These can be decoded into a person's brain-states and thoughts. The subject is then perfectly monitored from a distance.
NSA personnel can dial up any individual in the country on the Signals lntelligence EMF scanning network and the NSA's computers will then pinpoint and track that person 24 hours-a-day. The NSA can pick out and track anyone in the U.S.
NSA Signals Intelligence Use of EMF Brain Stimulation
NSA Signals Intelligence uses EMF Brain Stimulation for Remote Neural Monitoring (RNM) and Electronic Brain Link (EBL). EMF Brain Stimulation has been in development since the MKUltra program of the early 1950's, which included neurological research into "radiation" (non-ionizing EMF) and bioelectric research and development. The resulting secret technology is categorized at the National Security Archives as "Radiation Intelligence," defined as "information from unintentionally emanated electromagnetic waves in the environment, not including radioactivity or nuclear detonation."
Signals Intelligence implemented and kept this technology secret in the same manner as other electronic warfare programs of the U.S. government. The NSA monitors available information about this technology and withholds scientific research from the public. There are also international intelligence agency agreements to keep this technology secret.
The NSA has proprietary electronic equipment that analyzes electrical activity in humans from a distance. NSA computer-generated brain mapping can continuously monitor all the electrical activity in die brain continuously. The NSA records aid decodes individual brain maps (of hundreds of thousands of persons) for national security purposes. EMF Brain Stimulation is also secretly used by the military for Brain-to-computer link. (In military fighter aircraft, for example.)
For electronic surveillance purposes electrical activity in the speech center of the brain can be translated into the subject's verbal thoughts. RNM can send encoded signals to the brain's auditory cortex thus allowing audio communication direct to the brain (bypassing the ears). NSA operatives can use this to covertly debilitate subjects by simulating auditory hallucinations characteristic of paranoid schizophrenia.
Without any contact with the subject, Remote Neural Monitoring can map out electrical activity from the visual cortex of a subject's brain and show images from the subject's brain on a video monitor. NSA operatives see what the surveillance subject's eyes are seeing. Visual memory can also be seen. RNM can send images direct to the visual cortex. bypassing the eyes and optic nerves. NSA operatives can use this to surreptitiously put images in a surveillance subject's brain while they are in R.E.M. sleep for brain- programming purposes.
Capabilities of NSA operatives using RNM
There has been a Signals Intelligence network in the U.S. since the 1940's. The NSA, Ft. Meade has in place a vast two-way wireless RNM system which is used to track subjects and non-invasively monitor audio-visual information in their brain. This is all done with no physical contact with the subject. RNM is the ultimate method of surveillance and domestic intelligence. Speech and 3D sound, and subliminal audio can be sent to the auditory cortex of the subject's brain (bypassing the ears) and images can be sent into the visual cortex. RNM can alter a subject's perceptions, moods, and motor control.
Speech cortex/auditory cortex link has become the ultimate communications system for the intelligence community. RNM allows for a complete audio-visual brain-to-brain link or brain-to-computer link.
National Security Agency Signals Intelligence Electronic Brain Link Technology
NSA SigInt can remotely detect, identify and monitor a person's bioelectric fields.
The NSA's Signals Intelligence has the proprietary ability to remotely and non-invasively monitor information in the human brain by digitally decoding the evoked potentials in the 30-50 hz,.5 milliwatt electro-magnetic emissions from the brain.
Neuronal activity in the brain creates a shifting electrical pattern that has a shifting magnetic flux. This magnetic flux puts out a constant 30-50 hz, .5 milliwatt electromagnetic (EMF) wave. Contained in the electromagnetic emission from the brain are spikes and patterns called "evoked potentials.”
Every thought, reaction, motor command, auditory event, and visual image in the brain has a corresponding "evoked potential" or set of "evoked potentials." The EMF emission from the brain can be decoded into the current thoughts, images and sounds in the subject's brain.
NSA SigInt uses EMF-transmitted Brain Stimulation as a communications system to transmit information (as well as nervous system messages) to intelligence agents and also to transmit to the brains of covert operations subjects (on a non-perceptible level).
EMF Brain Stimulation works by sending a complexly coded and pulsed electromagnetic signal to trigger evoked potentials (events) in the brain, thereby forming sound and visual images in the brain's neural circuits. EMF Brain Stimulation can also change a person's brain-states and affect motor control.
Two-way Electronic Brain-Link is done by remotely monitoring neural audio-visual information while transmitting sound to the auditory cortex (bypassing the ears) and transmitting faint images to the visual cortex (bypassing the optic nerves and eyes, the images appear as floating 2-D screens in the brain).
Two-Way Electronic Brain Link has become the ultimate communications system for CIA/NSA personnel. Remote Neural Monitoring (RNM, remotely monitoring bioelectric information in the human brain) has become the ultimate surveillance system. It is used by a limited number of agents in the U.S. Intelligence Community.
RNM requires decoding the resonance frequency of each specific brain area. That frequency is then modulated in order to impose information in That specific brain area. The frequency to which the various brain areas respond varies from 3 Hz to 50 Hz. Only NSA Signals Intelligence modulates signals in this frequency band.
An example of EMF Brain Stimulation:
Brain Area
Bioelectric
Resonance
Frequency
Information Induced
Through Modulation
Motor Control Cortex
10 HZ
Motor Impulse Co-ordination
Auditory Cortex
15 HZ
Sound which bypasses the ears
Visual Cortex
25 HZ
Images in the brain, bypassing the eyes
Somatosensory Cortex
09 HZ
Phantom Touch Sense
Thought Center
20 HZ
Imposed Subconscious Thoughts
This modulated information can be put into the brain at varying intensities from subliminal to perceptible.
Each person's brain has a unique set of bioelectric resonance/entrainment frequencies. Sending audio information to a person's brain at the frequency of another person's auditory cortex would result in that audio information not being perceived.
The Plaintiff learned of RNM by being in two-way RNM contact with the Kinnecome group at the NSA, Ft. Meade. They used RNM 3D sound direct to the brain to harass the Plaintiff from 10/90 to 5/91. As of 5/91 they have had two-way RNM communications with the Plaintiff and have used RNM to attempt to incapacitate the Plaintiff and hinder the Plaintiff from going to authorities about their activities against the Plaintiff in the last twelve years.
The Kinnecome group has about 100 persons working 24-hours-a-day at Ft Meade. They have also brain-tapped persons the Plaintiff is in contact with to keep the Plaintiff isolated. This is the first time ever that a private citizen has been harassed with RNM and has been able to bring a lawsuit against NSA personnel misusing this intelligence operations method.
NSA Techniques and Resources
Remote monitoring/tracking of individuals in any location. inside any building, continuously, anywhere in the country.
A system for inexpensive implementation of these operations allows for thousands of persons in every community to be spied on constantly by the NSA.
Remote RNM Devices
a) NSA's RNM equipment remotely reads the evoked potentials (EEGs) of the human brain for tracking individuals and can send messages through the nervous system to affect their performance.
b) [Information missing from original]
c) RNM can electronically identify individuals and track then anywhere in the U.S. This equipment is on a network and is used for domestic intelligence operations, government security, and military base security, and in case of bioelectric warfare.
Spotters and Walk-Bys in Metropolitan Areas
a) Tens of thousands of persons in each area working as spotters and neighborhood/business place spies (sometimes unwittingly) following and checking on subjects who have been identified for covert control by NSA personnel.
b) Agents working out of offices can be in constant communication with Spotters who are keeping track of the NSA's thousands of subjects in public.
c) NSA Agents in remote offices can instantly identify (using RNM) any individual spotted in public whom is in contact with surveillance subject.
Chemicals and Drugs into Residential Buildings with hidden NSA-lnstalled and maintained plastic plumbing lines.
a) The NSA has kits for running lines into residential tap water and air ducts of subjects for the delivery of drugs (such as sleeping gas or brainwashing aiding drugs). This is an outgrowth of CIA pharmapsychology.
Brief Overview of Proprietary U.S. Intelligence/Anti- Terrorist Equipment Mentioned.
Fixed network of special EMF equipment that can read EEGs in human brains and identify/track individuals by using digital computers. ESB (Electrical Stimulation to the Brain) via EMF signal from the NSA Signals Intelligence is used to control subjects.
EMF equipment that gathers information from PC circuit boards by deciphering RF emissions thereby gaining wireless modem-style entry into any personal computer in the country.
All equipment hidden, all technology secret, all scientific research unreported (as in electronic warfare research).
Not known to the public at all, yet complete and thorough implementation of this method of domestic intelligence has been in place since the early 1980's.
Resources
These publications have only been discovered since December 1991, after Plaintiff had already notified authorities (Dept. of Justice, etc.) of Public Corruption by named NSA employees. When no action was taken against the NSA employees I researched the Intelligence Community electronic surveillance technology involved and discovered the following publications:
The Body Electric
Electromagnetism and the Foundation of Life, by Robert Becker, M.D.
p. 265/313/318. Monitoringeuroelectric information in the brain. E-M wave E.S.B.
Cross Currents, by Robert Becker, M.D.
p. 70, p. 78, p. 105/210/216/220/242/299/303 E-M ESB. Simulating auditory hallucinations. p. 274, "Remote computer tampering using the RF emissions from the logic board."
Currents of Death by Paul Brodeur
p. 27/93. Driving brain electrical activity with external E-M, Magnetophosphenes, Delgado.
The Zapping of America by Paul Brodeur
DoD E-M ESB Research, simulating auditory hallucinations.
Of Mice, Men and Molecules, by John H. Heller. 1963.
p. 110, Bioelectricity. probing the brain with E-M waves.
The 3-Pound Universe, by Judith Hooper
p. 29/132/137. CIA EEG research. EEG's for surveillance.
In the Palaces or Memory, by George Johnson
E-M emissions from the brain,the brain as an open electromagnetic circuit.
The Puzzle Palace, by James Bamford
Signals intelligence, most advanced computers in the early Sixties
The U.S. Intelligence Community -Glossary terms at National Security Archives:
Radiation intelligence - information from unintentionally emanated electromagnetic energy, excluding radioactive sources.
The Search for the "Manchurian Candidate," by John Marks
p. 327. Electrical or radio stimulation to the brain, CIA R&D in bioelectrics.
Secret Agenda, by Jim Hougan
National Security cult groups.
Crines of the Intelligence Commununity. by Morton Halperin
Surreptitious entries; intelligence agents running operations against government workers
War in the Age of Intelligent Machines
NSA computer supremacy, complete control of information
Alternate Computers, by Time-Life Books
Molecule Computers
The Mind, by Richard Restak, M.D.
p. 258, EEG Systems Inc., decoding brain E-M emanations, tracking thoughts on a computer.
MedTech, by Lawrence Gallon
Triggering events in the brain" direct to auditory cortex signals.
Cyborg, by D.S. Halacy, Jr. (1965)
Brain-to-computer link research contracts given out by the U.S. Govemment
Psychiatry and the C.I.A.: Victims of Mind Control by Harvey M. Weinstein. M.D.
Dr. Cameron, psychic driving. ultraconceptual communications.
Journey Into Madness: Ihe True Story of Secret CIA Mind Control and Medical Abuse, by Gordon Thomas
p. 127/276/116, 168-69. Intelligence R & D. Delgado. Psychic driving with radio telemetry.
Mind Manipulators, by Alan Scheflin and Edward M. Opton
MKULTRA brain research for information gathering
The Brain Changers, by Maya Pines.
p. 19. Listening to brain E-M emissions.
Modern Bielectricity
Inducing audio in the brain with e-m waves, DoD cover-up, E-M wave ESB. Remote EEGs.
Magnetic Stimulation in Clinical Neuropsysiology by Sudhansu Chokroverty
Magneto-Phosphenes. Images direct to the visual cortex.
The Mind of Man by Nigel Calder
U.S. Intelligence brain research
Neuroelectric Society Conference - 1971
Audio direct to the brain with e-m waves, two waf remote EEG.
Brain Control by Elliot S. Valenstein
ESB control of individuals
Towards Century 21 by C.S. Wallia
p. 21. Brain Stimulation for direct to brain communication.
Mind Wars by Ron McRae, associate of Jack Anderson
p 62/106/136. Research into brain-to-brain electronic communications, remote neural e-m detection.
Mind Tools by Rudy Rucker
Brain tapping, communication with varying biomagnetic fields. p. 82
U.S. News and World Report 1/2/84
p. 88. e-m wave brain stimulation. Intelligence community high tech.
Ear Magazine article on extremely low frequency radio emissions in the natural environment, radio emissions from the human body.
City Paper article on FCC and NSA "complete radio spectrum" listening posts. 1/17/92.
Frontiers in Science - 1958 - by Edward Hutchings, Jr.
p. 48
Beyond Biofeedback - 1977 - by Elmer and Alyce Green
p. 118
The Body Quantum by Fred Alan Wolf
Cloning - A Biologist Reports by Robert Gilmore McKinnell
Ethical review of cloning humans.
Hoover's FBI by former agent William Turner
p. 280. Routines of electronic surveillance work.
July 20, 2019 by Arthur C. Clarke
Lida, Neurophonics, Brain/Computer Link
MegaBrain by Michael Hutchison
p. 107/108/117/120/123. Brain stimulation with e-m waves. CIA research and information control.
The Cult of Information by Theodore Rosnak - 1986
NSA Directive #145. Personal Files in Computers. Computer automated telephone tapping
The Body Shop
1968 implantation of an electrode array on the visual cortex for video direct to the brain and other 1960s research into electronically triggering phosphenes in the brain, thus bypassing the eyes.
Evoked Potentials by David Regan
Decoding neuroelectric information in the brain
http://www.angelfire.com/or/
Angelfire - error 410
www.angelfire.com
Angelfire on Lycos, established in 1995, is one of the leading personal publishing communities on the Web. Angelfire makes it easy for members to create their own blogs, web sites, get a web address (domain) and start publishing online.
image source
http://pbs.twimg.com/media/
http://www.marketoracle.co.uk/
http://i.imgur.com/OyxjKfL.jpg
https://
https://ixquick-proxy.com/do/
http://parapolitics-info.
http://www.bibliotecapleyades.
https://ixquick-proxy.com/do/
http://humanoidolabs.blogspot.
DULY
ELECTED President Albert Gore Jr.awaits inauguration,our U.S.
Constitution that is theSupreme Law of the United Statesdemands it!
As we live free or die, Lafayette remains at Brandywine and
Albert Gore Jr. remains the year 2000,
U.S. CONSTITUTION DULY ELECTED, non-inaugurated,
natural born REAL President of the United States.
As we live free or die, Lafayette remains at Brandywine and
Albert Gore Jr. remains the year 2000,
U.S. CONSTITUTION DULY ELECTED, non-inaugurated,
natural born REAL President of the United States.
Al Gore on Restoring the Rule of Law
http://www.acslaw.org/acsblog/
http://www.acslaw.org/acsblog/